Security Firm Pokes Holes in Xfinity Home
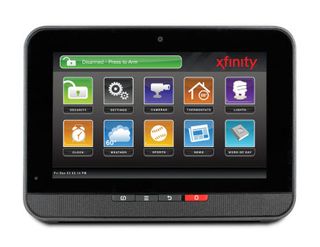
Comcast was put on the defensive last week when a security research firm said it found vulnerabilities in the Xfinity Home platform that could let outsiders hack in and wreak havoc.
Philadelphia-based Comcast, which has more than 500,000 Xfinity Home customers, said it is looking into the findings, but noted that its platform uses the same industry-standard systems as other providers. That means it could be an issue for the entire smart home and security sector, not just Comcast.
Rapid7, the company that put out the report, said would-be hackers could easily target the ZigBee-based wireless platform Comcast uses in the 2.4-Gigahertz band, which, Rapid7 claims, can be jammed to block communications between the Xfinity Home hub and other components of the home automation and security system, such as door sensors.
Xfinity Home “does not fail closed with an assumption that an attack is underway,” Rapid7 said. “Instead, the system fails open,” meaning that the sensors would believe that all sensors are intact, all doors are closed and no motion is detected. That improper state can last from anywhere from several minutes to three hours, it said.
There are a number of techniques available to cause interference or deauthenticate the underlying ZigBee-based communications protocol, Rapid7 said, including commonplace radio-jamming equipment.
“By creating a failure condition in the 2.4-GHz radio frequency band, the Comcast Xfinity Home Security System fails open, with the base station failing to recognize or alert on a communications failure with the component sensors,” the researchers said. “In addition, sensors take an inordinate amount of time to re-establish communications with the base station, even if their ‘closed’ state is switched to ‘open’ during the failure event.”
There are “no practical mitigations” to resolve the issue, Rapid7 said, holding that it might take a software or firmware update to the base station to determine how much and how long a radio failure condition should be tolerated, and how quickly sensors can re-establish communications with the base station.
Multichannel Newsletter
The smarter way to stay on top of the multichannel video marketplace. Sign up below.
Comcast said it will look into the findings, and intends to work with others in the homesecurity and automation sector on ways to handle the situation.
“Our home-security system uses the same advanced, industry-standard technology as the nation’s top home-security providers,” the operator said. “The issue being raised is technology used by all home security systems that use wireless connectivity for door, window and other sensors to communicate.
“We are reviewing this research and will proactively work with other industry partners and major providers to identify possible solutions that could benefit our customers and the industry.”
And it would seem that other systems could also be exposed by similar vulnerabilities.
In 2014, Oak Ridge National Lab and Qualys found similar jamming issues on systems from suppliers such as ADT and Vivint that also rely on radio signals between door and window sensors and control hubs.
The good news is that it’s still a relatively small problem. CNET reported last year that the odds of hackers bypassing a security system remain small enough that the FBI does not track those statistics.
But it’s an issue that will need to be solved as more consumers sign up and install these smart home platforms. The Consumer Technology Association predicts that the smart-home tech sector (including connected thermostats, cameras, smart locks and lighting) will reach 8.9 million units sold in 2016, a 21% increase, alongside $1.2 billion in revenue.
