Arris: Risks Posed by Modem Password Vulnerability ‘Low’
Arris said the risks are “low” with respect to a report from a Brazilian researcher who claims that about 600,000 cable modems from the supplier are vulnerable to previously undisclosed “backdoors” that could leave the devices open to hackers.
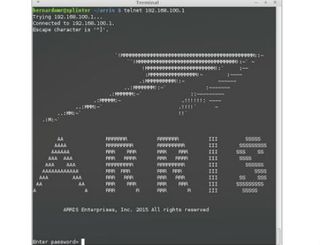
"While researching on the subject, I found a previously undisclosed backdoor on Arris cable modems, affecting many of their devices including TG862A, TG862G, DG860A," Bernardo Rodriques noted in this blog item posted November 19. He said the backdoor affects “over 600.000 externally accessible hosts.”
In an email to Multichannel News in response to Rodriques’s findings, Arris noted that the company had implemented this access method on certain cable modem products to provide access to technicians, but has since disabled that access in order to minimize any risks to subscribers.
“Security is a top priority at ARRIS,” the company said, in a statement. “When it comes to our network and customer premises equipment products, we work actively with security organizations and our Service Provider customers to identify and quickly resolve any potential vulnerabilities to protect the consumers who use our devices. We are aware of the recently reported password vulnerability. The risk related to this vulnerability is low, and we are unaware of any exploit related to it. However, we take these issues very seriously and review them with the highest priority. Our team has been working around the clock on modem updates that address this reported vulnerability.”
Per Rodriques’s findings, firmware in the affected modems shipped with an undocumented "libarris_password.so" library that essentially acted as a backdoor for privileged account logins that supplied a different custom password for each day of the year. “ARRIS password of the day is a remote backdoor known since 2009,” he explained.
A Comcast employee noted on the DSL Reports message board that the MSO does not use the Arris default password of the day, and filters external access to the modem.
However, a network engineer claiming to be with a “large MSO in Mississippi,” said the operator learned about the backdoors last week “and have been scrambling to close the holes.”
Multichannel Newsletter
The smarter way to stay on top of the multichannel video marketplace. Sign up below.
