News
Latest News

Freeze Frame: Cable Hall of Fame 2024 (Photo Gallery)
By Michael Demenchuk published
Images from the induction ceremony held April 18 at New York’s Ziegfeld Ballroom

NBA Playoffs Will Offer Viewers Something Familiar, Something New
By R. Thomas Umstead published
ESPN, TNT Sports hope mix of fresh teams, players and postseason stalwarts will drive ratings

Fremantle Hires Jeff Boone as VP, Scripted Development
By Jon Lafayette published
Exec had been at Bad Wolf

NHL, NBA Playoffs Begin; Haney-Garcia PPV Boxing Event: What’s on This Weekend in TV Sports (April 20-21)
By R. Thomas Umstead published
A look at the weekend's top TV sports events on broadcast, cable and streaming services

Hall of Fame Boxing Announcer Jim Lampley Chatting Up the Sweet Science on PPV.com (Q&A)
By R. Thomas Umstead published
Will host PPV.com’s live chat for the April 20 Devin Haney-Ryan Garcia PPV boxing event
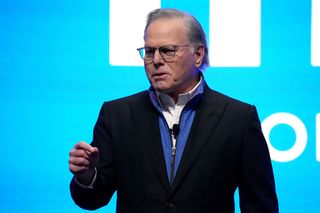
Warner Bros. Discovery CEO David Zaslav Got 27% Raise to $49.7 Million in 2023
By Jon Lafayette published
Other top WBD execs also saw their compensation increase

DAZN Weighs in With Content Ahead of Haney-Garcia Fight
By Jon Lafayette published
‘Run It Up’ is hosted by Rachel DeMita, Demetrious Johnson, Master Tesfatsion

Daytime Emmys Announce Some Nominations Early
By Paige Albiniak published
Entertainment magazines get early scoop in several categories
Multichannel Newsletter
The smarter way to stay on top of the multichannel video marketplace. Sign up below.





